Remember the days when you had to wade through boxes of paper documents to build a case? Sure, we still gather information this way — but the internet has helped make data collection a more digital affair.
From email to social media posts, everyone has a virtual footprint. As a legal professional, you’ll look online for evidence as you prepare for a day in court.
The digital clues needed come from electronically stored information (ESI). And this is not as simple as taking a screenshot of a file and saving it to your phone — the data needs to be identified, collected, stored, reviewed, and presented in the right way.
This is the eDiscovery process. Worldwide, the eDiscovery market is big business — set to hit a value of 17.1 billion US dollars by 2027.
You probably have some questions, so you’re in luck! In this article, I’ll talk about eDiscovery and the type of data it covers. I’ll also give you a rundown of the Electronic Discovery Reference Model (EDRM) and explain the rules.
Ready? Let’s go.
What Is eDiscovery?
EDiscovery, or electronic discovery, is commonly used in legal proceedings.
While you investigate a case, your legal team will collect evidence from a range of sources.
The eDiscovery process involves looking for evidence in ESI. This evidence could be found in a text message, email, word document, or calendar appointment.
The eDiscovery process includes only digital data; it doesn’t include any paper documents, interviews, or testimonies. Though these traditional methods are still important, they simply don’t fit under the eDiscovery umbrella.
Your digital investigations can help you uncover information, facts, and timelines. Of course, every hard drive is packed with data, and a lot of it is often irrelevant.
A step-by-step method called EDRM can help you make the most of the eDiscovery process and find what you need. I’ll explain each phase of it later in this article.
What Are the Benefits of eDiscovery?
Technology is changing quickly, and while eDiscovery is streamlining the way legal professionals prepare for court, not everyone has jumped on the bandwagon.
In fact, only 32.9% of law firms use software for evidence preparation and management. Despite this, 54.4% of attorneys say they need to regularly review ESI.
Now, if you’re not convinced, I’m here to tell you there are clear benefits of eDiscovery. Taking advantage of new technology that others haven’t yet embraced will give you a competitive edge.
When you use eDiscovery, you can save time. With all the data in one place, you can easily search for what you need.
Your team will also be more efficient and accurate in their findings. Why? Because a digital footprint can’t be disputed. You’re not relying on someone telling the “truth” verbally.
For example, if a client takes a photo at three o’clock on a Tuesday and uploads it to Facebook, it’ll come with metadata. Dates, times, and locations can all be verified, giving the client a virtual alibi.
Plus, since eDiscovery is a process, the information is accessed, reviewed, and analyzed.
What Type of Data Is Included?
The eDiscovery process can involve a range of data types. Here are some examples of what can be used in litigation:
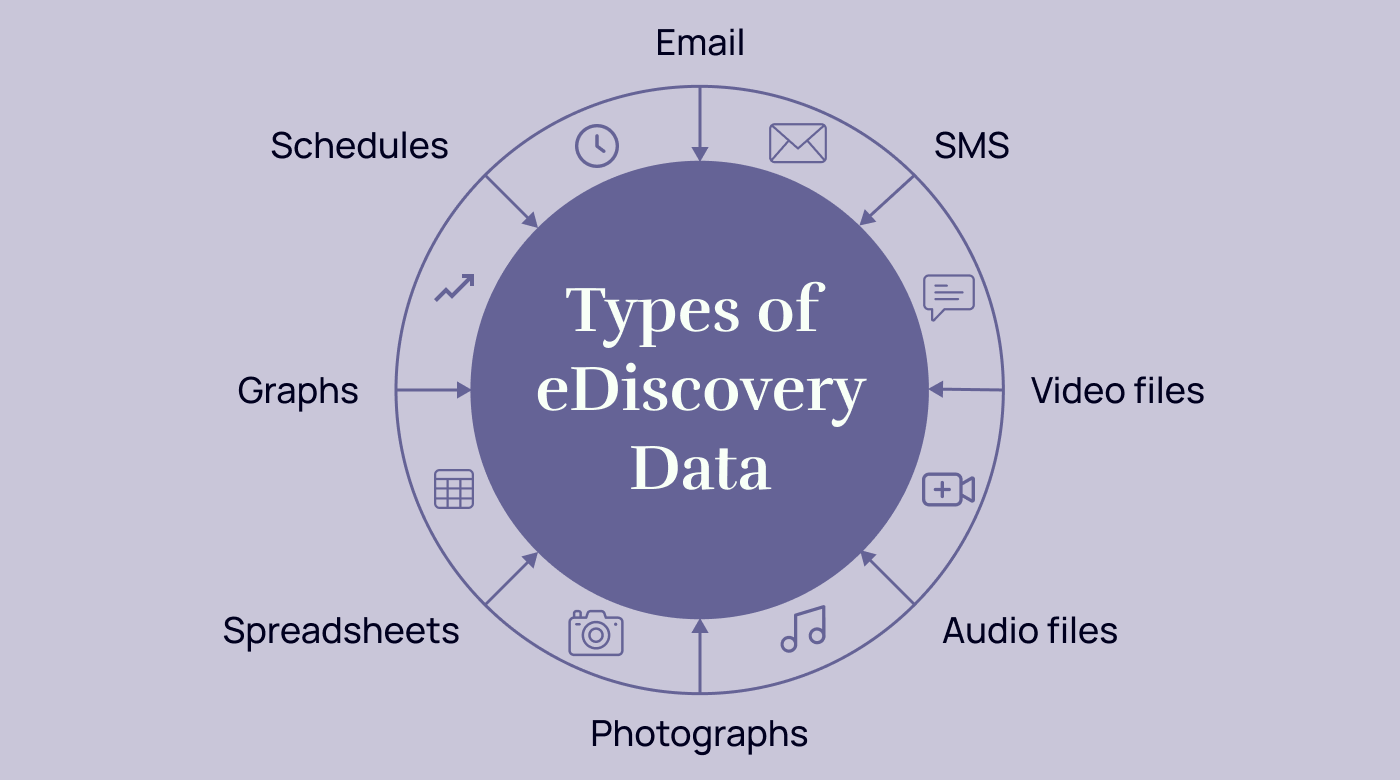
Written Communication
During the eDiscovery process, you may get access to important written communication. This type of communication is often active data and includes emails and text messages.
SMS and email aren’t the only ways people send messages to one another. For example, WhatsApp has more than 2 billion users from across the globe.
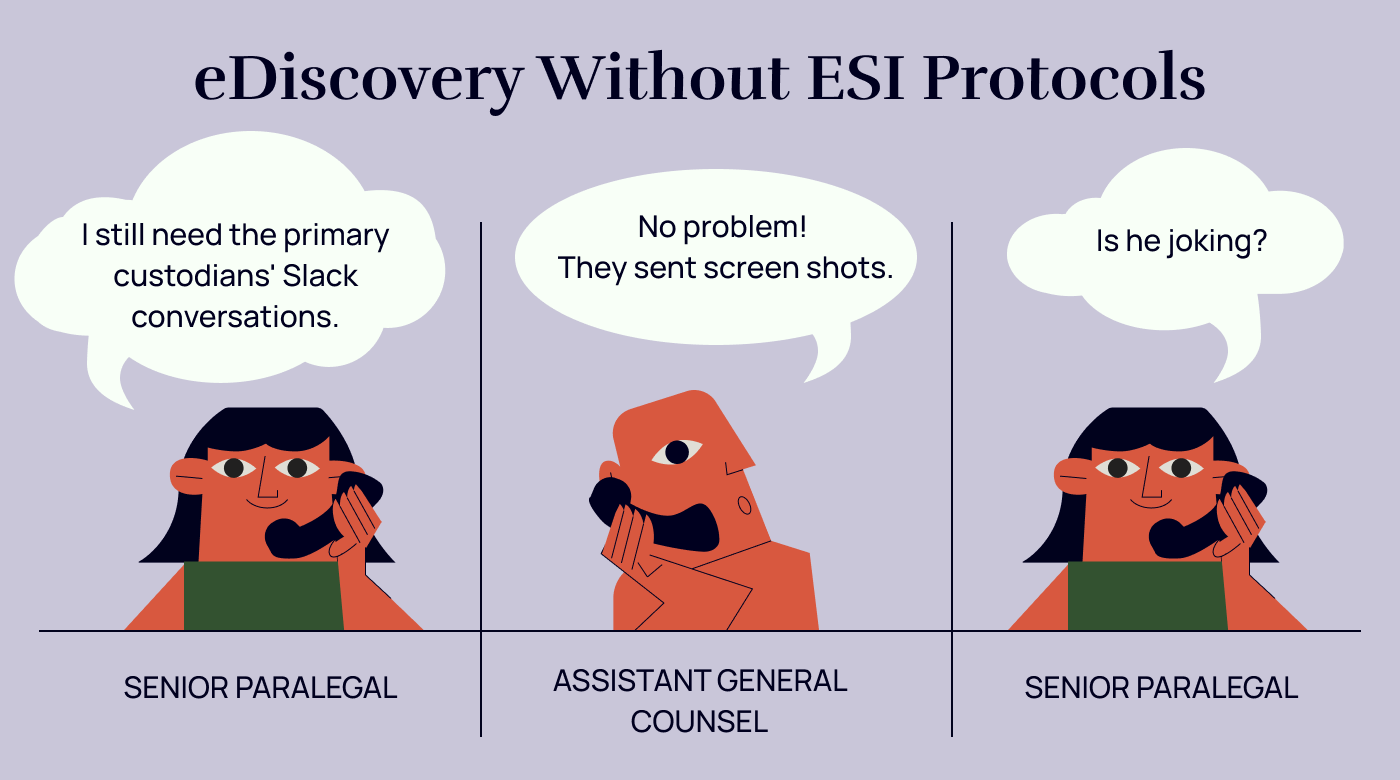
While all these types of ESI can support your case, there are challenges. A simple screenshot of a message won’t be enough because the conversations will need to be verified. Due to the nature of platforms like WhatsApp, a forensic specialist may need to be called in to authenticate the data.
There’s also more general written ESI, including documents, letters, and calendars accessible.
Visual Communication
Relevant electronic files may also include different types of visual communication. You’ve heard the saying, “A picture is worth a thousand words,” and this is also true when considering the evidence.
For example, digital photographs are frequently used in litigation. A photo can prove someone was at a certain place at a certain time or had a relationship with a key witness. Videos can also support your case — and may even show someone committing a crime.
Videos and photographs are useful because they have metadata, including timestamps and locations.
If the case relies on financial records, evidence is often found in spreadsheets and graphs. You can also look at digital drawings.
Verbal Communication
As a lawyer, you have excellent verbal communication skills. But our clients and witnesses don’t always have the same confidence in public speaking. And even if they recall specific conversations, dates, times, and contexts can get mixed up.
Fortunately, digital forms of verbal communication can help to tell the story. When you preserve metadata, these digital file formats can’t be disputed.
For example, there are voicemails. Let’s say your client has an abusive ex, and there are hundreds of threatening voicemail messages from them. These messages can be preserved and used to support your case.
Alternatively, there may be voice recordings. You may even get lucky and find a taped confession. Of course, if they’re secret recordings, they may not be admissible. The answer will depend on your location and how relevant evidence is to the case.
Social Media
Social media keeps us connected. And when you dig into someone’s online behavior, you can uncover electronic evidence.
Let’s use Facebook as an example.
Facebook is a popular platform. By 2027, it’s predicted there’ll be 254.26 million users of this platform in the United States.
With this kind of widespread use, it makes sense to examine social media data as part of the eDiscovery process. There may be photos, private messages, status updates, tags, check-ins, and videos that are relevant to a case.
And Facebook isn’t the only useful social media site. There’s X (formerly Twitter), Instagram, Tiktok, and more.
Once again, if social media is part of your eDiscovery mix, everything you use needs to be authentic and verifiable.
Metadata
Metadata, which is everywhere, is used to authenticate other evidence.
For example, if you have a photograph on your phone, it’ll say who took it, where, and when. Your job will be to establish the “why.”
It can be difficult to preserve metadata, but it’s essential if you want it to be part of your evidence.
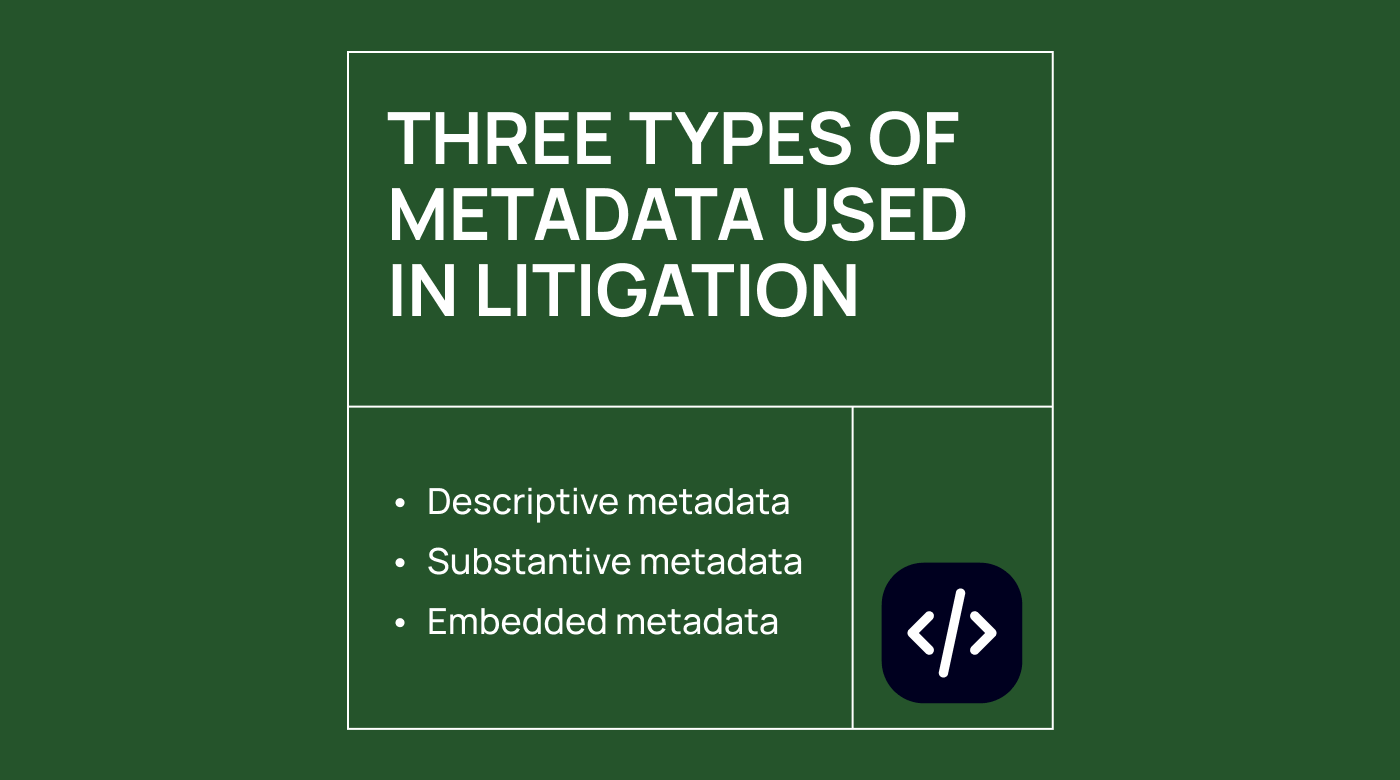
There are three types of metadata you can look at. They are as follows:
- System metadata: records created by the operating system to show when a file was made or modified
- Substantive metadata: records of any changes made to documents by the user
- Embedded metadata: hidden data that’s embedded in individual files
What Is the EDRM Process?
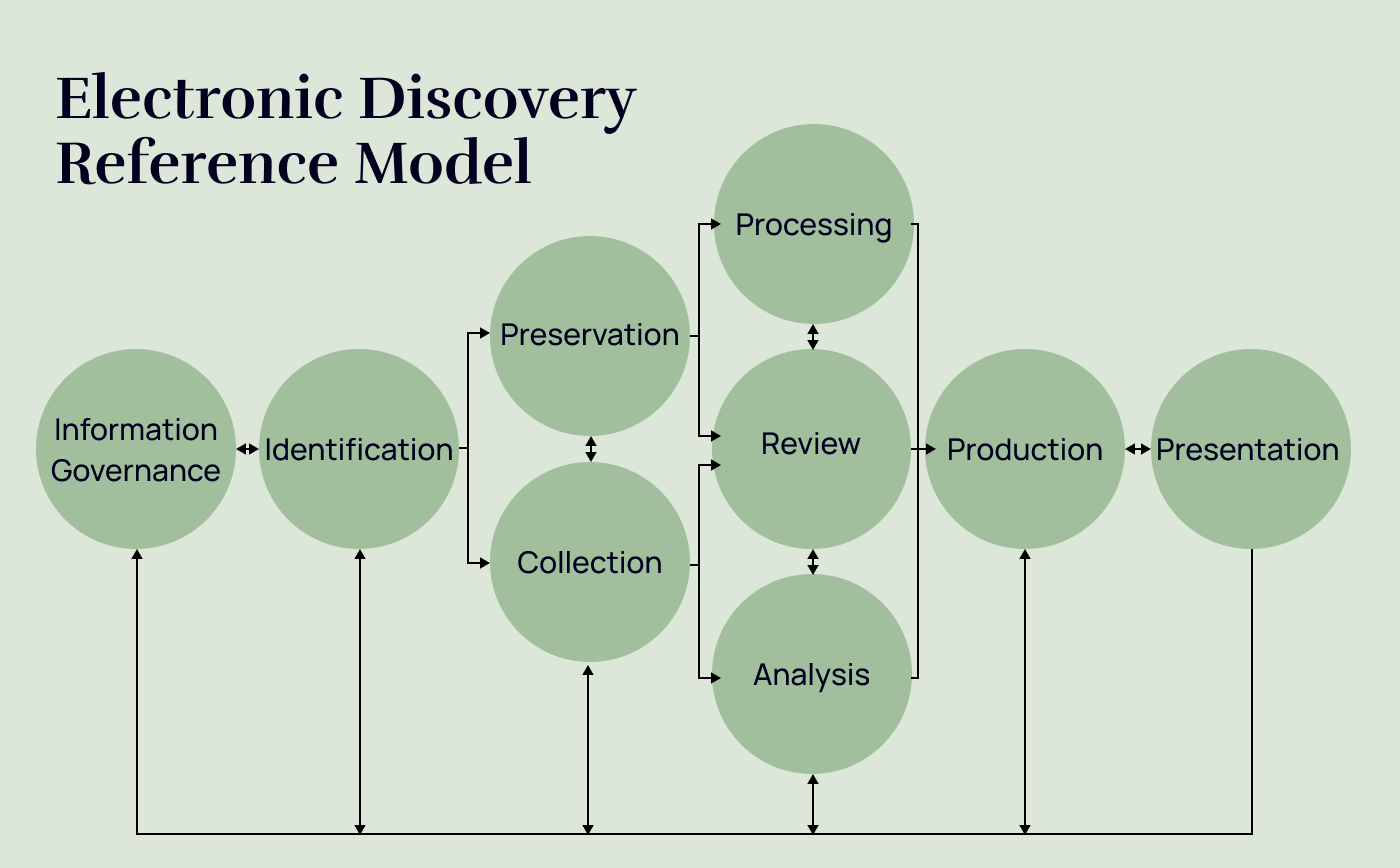
In 2005, George Socha and Tom Gelbmann created the Electronic Discovery Reference Model (EDRM). The process has evolved since then, but the general idea is still the same.
There are nine eDiscovery stages, and some of them can overlap. Here’s each step and what you can expect during it:
1. Information Governance
Information governance (IG) is the newest addition to the EDRM process. It’s a critical component and something you need to think about throughout the entire eDiscovery process.
So, what’s IG all about?
EDiscovery involves dealing with sensitive and confidential data, and you need to be compliant. IG covers best practices, starting with your policies and procedures.
Your policies need to be detailed because there are a lot of bases to cover. For example, you’ll need to have clear guidelines for data privacy, security, storage, and sharing.
If you have a remote team, you’ll need to decide how you can work without putting the data at risk.
Even with strong security measures in place, breaches can happen, and you can end up with lost data. Your IG policies and procedures should include strategies for dealing with unexpected events.
2. Identification
Every case is different, so the types of digital evidence you’ll need can vary. During the identification stage, you need to decide what you’re looking for.
Due to the scale of ESI, it’s almost impossible to download every single piece of data and go through it manually. That’s like looking for a needle in a haystack.
First, you can review the case and look at the facts. What types of digital files would be relevant? Talk to witnesses, and try to follow the trail to narrow down your search.
For example, you may be looking for secret emails, suggestive text messages, or unexplained meetings on a calendar.
3. Preservation
If it looks like litigation is inevitable, you’ll need to preserve any relevant documents. For the ESI to stand up during legal procedures, it can’t be changed or deleted.
A “legal hold” — which blocks the removal or modification of ESI — can be put on the data, with potential fines if the information is tampered with.
There are three ways to preserve data depending on your budget and the size of your practice:
- Asking for the data to remain untouched until you need it
- Creating a backup of the relevant ESI
- Installing software to preserve the data without having to remove it
The most important thing is to keep the ESI secure until it’s time to collect it. One lost file could impact your entire strategy.
4. Collection
The collection phase is closely linked to the preservation phase. You’ll need to flag any relevant ESI and make sure it’s all in one place so that it’s easy to access.
If you have an IT department, it’ll be their job to safely transfer the data to a secure location. Alternatively, you can outsource this process.
You’ll collect different types of ESI, including cloud-based, hidden, and mobile data. Remember, you don’t need to collect everything because too many files will only leave you feeling overwhelmed — and overworked.
I’ve said it before, but here’s a reminder: the metadata needs to stay intact, and you’ll need to refer to your ESI protocols from the IG stage.
5. Processing
Next is the processing phase. This step is where you’ll really start to narrow down your search for relevant evidence.
Even if you’ve been selective, there’ll still be a lot of data to sort through. Some of the ESI may be duplicated, so you’ll need to remove any double-ups.
During this step, the ESI needs to be put into a format that’s accessible to your team. You can use dedicated software to streamline your processes. For example, some legal firms use ESI review platforms. Or, if the amount of ESI is small, you can merge the data into a PDF file.
Over time, new ESI may become relevant. You should be prepared to revisit the collection phase throughout the litigation.
You can improve accuracy during this stage with technology. Take a look at this guide I created containing the top legal document comparison software options.
6. Review
During the review stage, all of the remaining data needs to be looked at.
If there is an extensive amount of ESI, reviewing it all can be time-consuming. You’ll be looking for anything that may be useful to your case. Keep in mind that if you have processed it correctly, the review process will be much easier.
Sometimes, this step is outsourced, and the data is returned for analysis. Law firms may also use artificial intelligence (AI) to sort through the information. You’ll need to set search parameters so the program knows what to look for. Even if you do use AI, some manual reviews will still be necessary.
Whether you have an in-person team or use other methods for review, make sure you follow your IG policies.
7. Analysis
By now, the relevant ESI will be in one place, reviewed, and ready for analysis. You’ll have started to gather evidence as you prepare your case.
During the analysis phase, you can begin to link the data to your case by looking for patterns, putting items in order of their importance, and creating timelines.
Later on, you can see if anything’s been missed. For example, there may be a page missing from a PDF or a text message thread that’s broken. Or you may find clues about other documents to look for.
If you find that you need to go back to the processing stage to gather more evidence, now is the time to do so.
Legal case analysis software can also be beneficial during this step.
8. Production
Once you’ve analyzed the ESI, the defense will start to take shape. You’ll know what’s relevant and where everything fits in the litigation.
The production phase is toward the end of the EDRM process. Your team will prepare the evidence for the legal process. The court may ask for the evidence to be in a specific format, and you should keep that in mind when collating your information.
This stage is mainly administrative and does take time and attention to detail. All of the information needs to be looked over and sorted into categories.
Documents need to be numbered and stamped, and redactions may be required. When the evidence is ready, you’ll share it with the relevant parties — including your opponent.
I’ll talk about software trends later in the article, but rest assured that there are solutions available to make the production process efficient.
9. Presentation
Finally, it’s time for the presentation phase. Once you’ve reached this point, you can prepare the ESI for the trial.
Traditional methods can support your digital file presentations. Things like witness testimonies, physical evidence, and expert statements won’t ever be replaced.
Think about how you’ll present the data in court. The strategy you use will depend on the type of data you want to share. For example, you can use videos, slide shows, or graphics.
What Are the Rules of eDiscovery?
Access to electronic records has changed the way we practice law. But with the perks come responsibilities, and there are a few eDiscovery rules you’ll need to follow.
You’re a legal professional, so I know many of these rules will feel like common sense — in fact, they’re probably things you do naturally. However, it’s always worth going over the fine print.
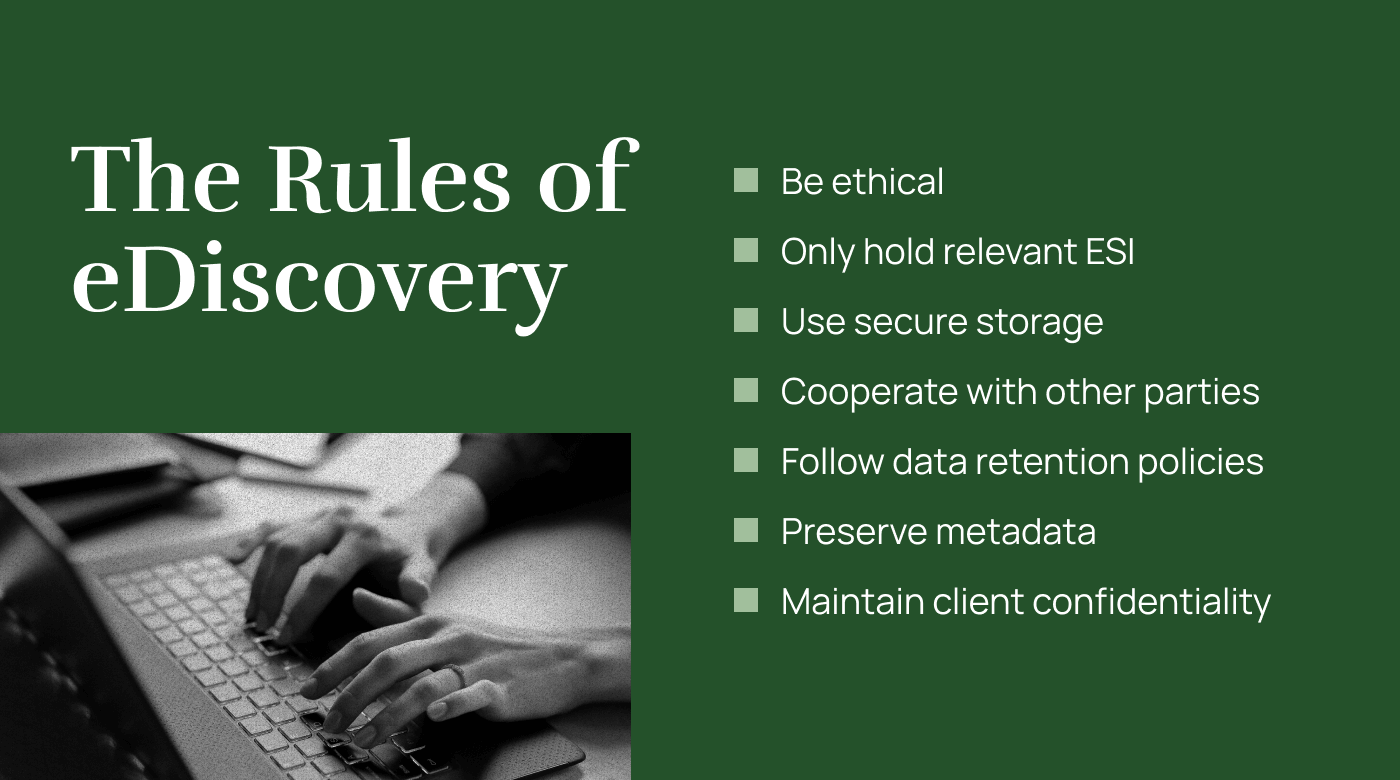
You need to be ethical. You’ll have access to personal data, and most of it won’t be relevant to litigation. Only hold onto ESI if it’s potential evidence. An audio file of a meeting may be relevant, while a photo of a cute dog probably won’t be.
The way you store the information needs to be secure, and it’s important to follow data retention policies. These strategies will be part of the IG phase, but you’ll have to keep monitoring your processes over time.
Remember, all devices need to be maintained, and staff should use secure networks and update their passwords regularly.
You’ll need to cooperate with other relevant parties and be careful to preserve metadata.
And, of course, client confidentiality should also be a priority.
The information you view should always be treated with respect and be kept private unless necessary for the case.
What Are the Risks of eDiscovery?
I’ve told you about the rules, but what about the risks? What can go wrong when you rely on the eDiscovery process?
You know you need to maintain data security, but what can happen if you don’t? Electronic documents are vulnerable, especially when stored on a network. If there is a breach, sensitive data becomes susceptible to leaks.
Viruses can impact your access to documents and corrupt important files. You could lose evidence in the process.
Another factor to consider is the price tag. When you’re just starting out with eDiscovery, setting up your processes is an expensive undertaking. It may require investment in matter management software and team training/upskilling, which creates additional short-term work. However, the benefits are worth it, as the litigation becomes more efficient.
Even though eDiscovery is a digital process, there’s still room for human error. If your team is inexperienced, mistakes can happen. From accidentally deleting ESI to damaging metadata, any errors can affect your entire legal strategy.
If you do want to dive into eDiscovery but it’s not something you’re familiar with, I recommend investing in training for your IT team. Alternatively, there are options to outsource until you’re ready to use eDiscovery in-house.
What Is Digital Forensics?
Is digital forensics another word for eDiscovery?
The two may sound interchangeable, but they’re not the same thing.
Put simply, the ESI you find during the eDiscovery process will be readily available. It’ll usually be enough for use in most legal proceedings. The process is something anyone on your team can master — and with minimal training.
On the other hand, digital forensics is its own field, and experts are highly trained and skilled in the area.
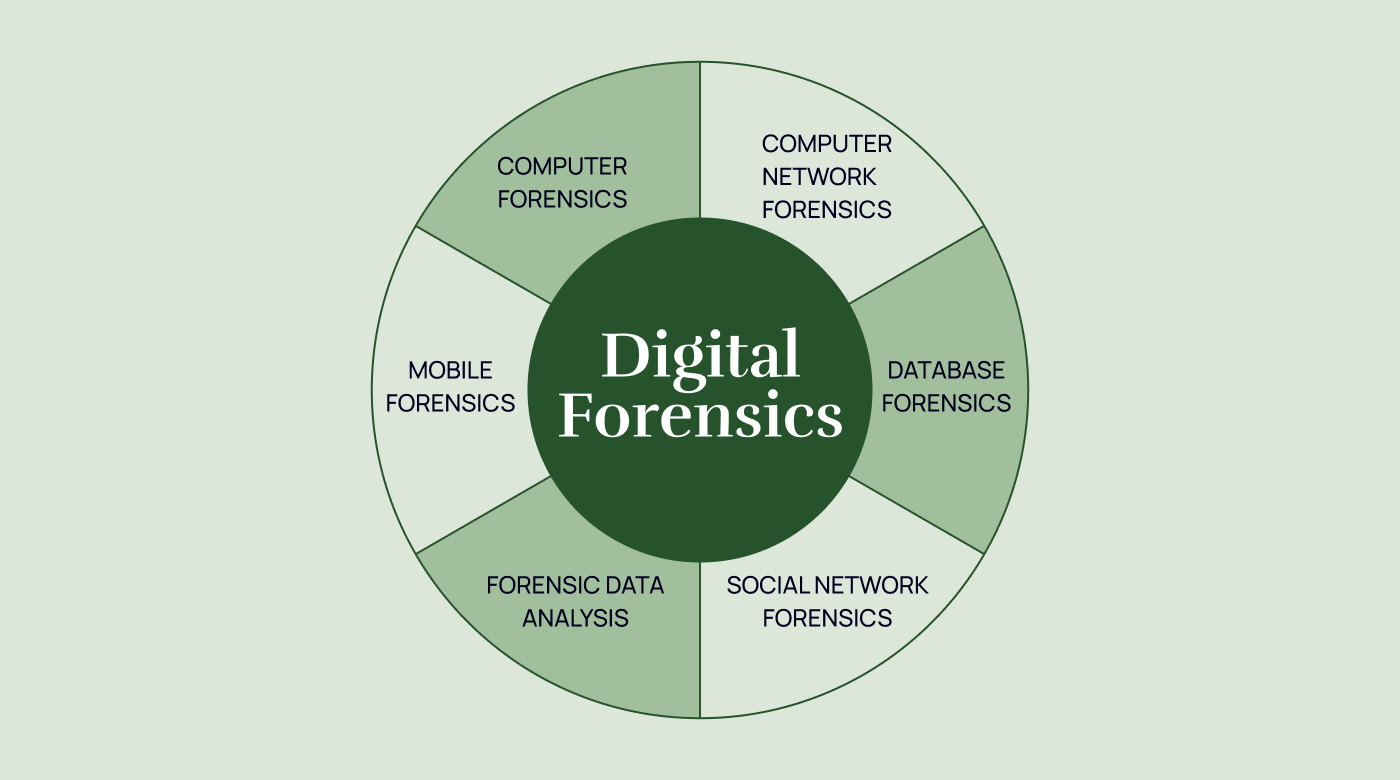
A digital forensics investigator is more interested in what’s hiding under the surface. They usually work with law enforcement agencies as part of criminal investigations, but they can also support law firms.
These professionals use software and other tools to uncover data that might otherwise be lost forever. For example, while an incriminating file may have been deleted, moved, or modified, a digital forensic investigator can help retrieve the original document. These forensic experts know how to find information that’s hidden on hard drives and storage chips.
Occasionally, there may be ESI that you know exists — but is nowhere to be seen. Unless you or someone on your team knows how to play the digital forensics game, you’ll need to call in an expert.
eDiscovery Software Trends
No one is expecting you to do all of this on your own. eDiscovery teams rely on software — every step of the way.
Storing big pools of data in-house is costly and comes with security risks. Because of this, law firms are switching to cloud-based solutions. When the software is in the cloud, it can be updated in real-time, and you can scale your package depending on your needs at the time.
You may have also noticed that AI is the talk of the town. It may sound like something from a sci-fi movie, but the future is already here. A robot isn’t about to stand up in court, but AI-powered tools can help us all work more efficiently.
But how?
For one thing, AI can help with predictive coding. This means you can use it to filter vast amounts of ESI and flag anything that may be relevant to the litigation. AI can analyze data so that you don’t have to. Think of it as an efficient search tool that can help you prepare for the document review stage in the EDRM process.
There are different options available, but I’ll use the Microsoft Purview eDiscovery platform as an example. There are different levels to the Purview software, and you can choose the features you need depending on your caseload and budget.
The Microsoft Purview platform lets you create an automated workflow. From preservation to collection to review, the data is scanned for you. Any relevant material is placed into a holistic map, ready for you to analyze.
Here’s a quick look at how the Microsoft Purview process works:
- Establish permissions.
- Identify and preserve ESI.
- Create a collection.
- Manage and review the content.
- Export the data.
- Prepare for review.
If you want more options, I’ve put together a list of the top eDiscovery tools. This guide covers Nextpoint, IPRO, Sightline, Everlaw, Epiq Discovery, Logikcull, RelativityOne, Smarsh, DISCO, and Ricoh. It includes pros and cons, features, and more.
And, while I’m talking about tech, you can try these legal research tools.
Before you sign up for an eDiscovery platform service, make sure it’s compliant and secure. Outsourcing doesn’t mean you’re not accountable if something goes wrong. Before you decide on a product, do your research and consider the features you need.
Making the Most of the eDiscovery Process
EDiscovery can support your litigation efforts within a wide range of needs. Scanning digital data gives you evidence that otherwise wouldn’t be available to you in such an efficient manner.
EDRM can help you extract the most out of the eDiscovery process. Remember, there are nine steps, and some of them can overlap. It starts with IG, followed by identification, preservation, collection, processing, and review.
Next comes the analysis stage, followed by production and presentation in court.
Different software applications can help streamline your workflows. AI and cloud-based solutions can take the pressure off your in-house teams, providing automation and freeing up their time.
Remember, compliance and security will be a top priority. You’ll be dealing with sensitive data, which requires careful preservation and confidentiality.
And while they are not needed often, occasions will occur when a digital forensic investigator is necessary. These experts can locate hidden or deleted data more efficiently and accurately than AI-powered software can.